Set up your first SSH keys
- Generate Ssh Key With Specific Name
- Generate Ssh Key With Different Name
- Generate Ssh Key Putty
- Generate Ssh Key Different Name In Word
- Generate Ssh Key Github
- Generate Ssh Key Different Name Labels
The following command creates an SSH key pair using RSA encryption and a bit length of 4096: ssh-keygen -m PEM -t rsa -b 4096 If you use the Azure CLI to create your VM with the az vm create command, you can optionally generate SSH public and private key files using the -generate-ssh-keys option. The user name is a comment, you can delete it or set it with the -C option. I do not see a host name anywhere in the keys, what file are you looking at? Ssh-keygen -f test -C noname Generating public/private rsa key pair. Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in test.
Generating SSH key pair consists of two basic phases. The first phase is generating the key pair on the local side, the second phase is copying it to the remote host, registering in the server and configuring the ssh daemon to make it useful. A key pair consists of two files, idrsa and idrsa.pub which are private and public keys respectively. Add your SSH private key to the ssh-agent and store your passphrase in the keychain. If you created your key with a different name, or if you are adding an existing key that has a different name, replace idrsa in the command with the name of your private key file. $ ssh-add -K /.ssh/idrsa.
Use SSH keys for authentication when you are connecting to your server, or even between your servers. They can greatly simplify and increase the security of your login process. When keys are implemented correctly they provide a secure, fast, and easy way of accessing your cloud server.
Follow our guide and learn how to set up your first SSH keys for authentication using OpenSSH or PuTTYTray.
Preparing your server
To add an SSH key pair, first, create a hidden folder to your user account home directory on your cloud server with the following command.
Then restrict the permissions to that directory to just yourself with the command below.
This creates a secure location for you to save your SSH keys for authentication. However, note that since the keys are stored in your user home directory, every user that wishes to connect using SSH keys for authentication has to repeat these steps on their own profile.
Using OpenSSH to generate a key pair
Now continue on your own computer if you are using Linux or any other OS that has OpenSSH. PuTTY users should skip to the next section.
1. Generate a new key pair in a terminal with the next command
The key generator will ask for location and file name to which the key is saved to. Enter a new name or use the default by pressing enter.
2. (Optional) Create a passphrase for the key when prompted
This is a simple password that will protect your private key should someone be able to get their hands on it. Enter the password you wish or continue without a password. Press enter twice. Note that some automation tools might not be able to unlock passphrase-protected private keys.
3. Copy the public half of the key pair to your cloud server using the following command
Replace the user and server with your username and the server address you wish to use the key authentication on.
This also assumes you saved the key pair using the default file name and location. If not, just replace the key path ~/.ssh/id_rsa.pub above with your own key name.
Enter your user account password for that SSH server when prompted.
You can now authenticate to your server with the key pair, but at the moment you would need to enter the passphrase every time you connect.
4. (Optional) Set up SSH Agent to store the keys to avoid having to re-enter passphrase at every login
Enter the following commands to start the agent and add the private SSH key.
Type in your key’s current passphrase when asked. If you saved the private key somewhere other than the default location and name, you’ll have to specify it when adding the key.
Afterwards, you can connect to your cloud server using the keys for authentication, and only having to unlock the key by repeating the last 2 steps once after every computer restart.
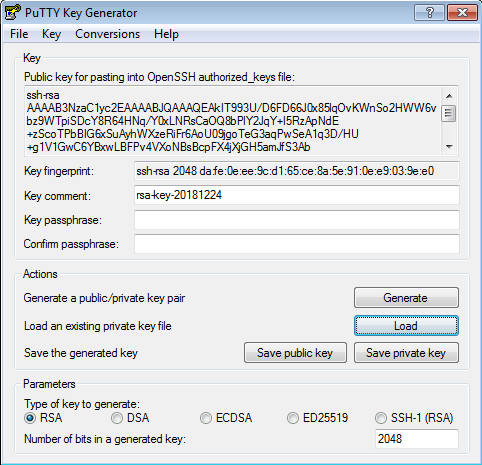
Using PuTTYTray to generate a key pair
If you are running Windows and PuTTYTray for SSH, you can use the built-in key generator from PuTTY to create a new key pair.
1. Click the Keygen button at the bottom of the PuTTY Configuration window to get started.
Then in the Key Generator window, check that the Type of key to generate at the bottom is set to SSH-2 RSA. The older SSH-1 was the first version on the standard but is now generally considered obsolete. Most modern servers and clients support SSH-2.
2. Click the Generate button to begin.
3. Keep moving your mouse over the blank area in any manner to help generate randomness for a few moments until the progress is complete.
With the keys finished, PuTTY will show the relative information about the pair along with the public key for easier copying.
4. (Optional) Enter a key passphrase in the 2 empty fields for the added security before continuing. The passphrase will protect your key from unauthorized use should someone be able to copy it. However, some automation tools might not be able to unlock passphrase-protected private keys.
5. Click the Save private key button and store it somewhere safe. Generally anywhere in your user directory is fine as long as your PC is password protected. Before closing the keygen, you may want to copy the public key to your clipboard, but you can always get it later as well.
Now that you have a new key saved on your computer, you’ll need to import it into the PuTTY key agent.
6. Click the Agent button to open the key manager in the PuTTY Configuration window.
7. Click Add Key button in the Key List, then browse to the location you saved the private key, select it and click Open.
Enter your key passphrase if asked.
This will import the key to your PuTTY client, but you still need to copy the public key over to your server.
8. Open an SSH connection to your cloud server and go to the SSH key directory.
9. Open or create the default file OpenSSH looks for public keys called authorized_keys.
10. Paste the public key into the file by simply right-clicking the SSH client window. Make sure the key goes on a single line for OpenSSH to be able to read it.
When you’ve copied the public key over to the authorized keys list, save the file and exit the editor. You can now test the public key authentication by logging in to your server again. You should not get asked for your password, but instead logged straight in with the key. If it’s not working, check that your private key is unlocked at your SSH Agent and try again.
Turn off password authentication
With SSH key authentication configured and tested, you can disable password authentication for SSH all together to prevent brute-forcing. When logged in to your cloud server.
1. Open the SSH configuration file with the following command.
2. Set the password authentication to no to disable clear text passwords.
3. Check that public key authentication is enabled, just to be safe and not get locked out from your server. If you do find yourself unable to log in with SSH, you can always use the Web terminal at your UpCloud control panel.
Then save and exit the editor.
4. Restart the SSH service to apply the changes by using the command below.
With that done your cloud server is now another step along towards security. Malicious attempts to connect to your server will results in authentication rejection, as plain passwords are not allowed, and brute-forcing an RSA key is practically impossible.
Conclusions
Remember to always keep your private keys safe. You can use the same key from multiple computers if you wish, or generate new ones on each client connecting to your cloud server for added security. Each user should generate their own key pair and passphrase for secure access control. With proper management, even in case one of the private keys gets compromised you won’t have to replace them all.
Generate Ssh Key With Specific Name
-->Azure Repos Azure DevOps Server 2019 TFS 2018 TFS 2017 TFS 2015 Update 3
Connect to your Git repos through SSH on macOS, Linux, or Windows to securely connect using HTTPS authentication. On Windows, we recommended the use of Git Credential Managers or Personal Access Tokens.
Important /windows-8-64-bit-key-generator.html.
SSH URLs have changed, but old SSH URLs will continue to work. If you have already set up SSH, you should update your remote URLs to the new format:
- Verify which remotes are using SSH by running
git remote -vin your Git client. - Visit your repository on the web and select the Clone button in the upper right.
- Select SSH and copy the new SSH URL.
- In your Git client, run:
git remote set-url <remote name, e.g. origin> <new SSH URL>. Alternatively, in Visual Studio, go to Repository Settings, and edit your remotes.
Note
As of Visual Studio 2017, SSH can be used to connect to Git repos.
How SSH key authentication works
SSH public key authentication works with an asymmetric pair of generated encryption keys. The public key is shared with Azure DevOps and used to verify the initial ssh connection. The private key is kept safe and secure on your system.
Set up SSH key authentication
The following steps cover configuration of SSH key authentication on the following platforms:
- Linux
- macOS running at least Leopard (10.5)
- Windows systems running Git for Windows
Configure SSH using the command line. bash is the common shell on Linux and macOS and the Git for Windows installation adds a shortcut to Git Bash in the Start menu.Other shell environments will work, but are not covered in this article.
Step 1: Create your SSH keys
Note
If you have already created SSH keys on your system, skip this step and go to configuring SSH keys.
The commands here will let you create new default SSH keys, overwriting existing default keys. Before continuing, check your~/.ssh folder (for example, /home/jamal/.ssh or C:Usersjamal.ssh) and look for the following files:
- id_rsa
- id_rsa.pub
If these files exist, then you have already created SSH keys. You can overwrite the keys with the following commands, or skip this step and go to configuring SSH keys to reuse these keys.
Create your SSH keys with the ssh-keygen command from the bash prompt. This command will create a 2048-bit RSA key for use with SSH. You can give a passphrasefor your private key when prompted—this passphrase provides another layer of security for your private key.If you give a passphrase, be sure to configure the SSH agent to cache your passphrase so you don't have to enter it every time you connect.
This command produces the two keys needed for SSH authentication: your private key ( id_rsa ) and the public key ( id_rsa.pub ). It is important to never share the contents of your private key. If the private key iscompromised, attackers can use it to trick servers into thinking the connection is coming from you.
Step 2: Add the public key to Azure DevOps Services/TFS
Associate the public key generated in the previous step with your user ID.
Open your security settings by browsing to the web portal and selecting your avatar in the upper right of theuser interface. Select Securityhttps://duoever246.weebly.com/blog/tuxera-ntfs-for-mac-download. in the menu that appears.
Select SSH public keys, and then select + New Key.
Copy the contents of the public key (for example, id_rsa.pub) that you generated into the Public Key Data field.
Important
Avoid adding whitespace or new lines into the Key Data field, as they can cause Azure DevOps Services to use an invalid public key. When pasting in the key, a newline often is added at the end. Be sure to remove this newline if it occurs.
Give the key a useful description (this description will be displayed on the SSH public keys page for your profile) so that you can remember it later. Select Save to store the public key. Once saved, you cannot change the key. You can delete the key or create a new entry for another key. There are no restrictions on how many keys you can add to your user profile.
Step 3: Clone the Git repository with SSH
Note
To connect with SSH from an existing cloned repo, see updating your remotes to SSH.
Copy the SSH clone URL from the web portal. In this example, the SSL clone URL is for a repo in an organization named fabrikam-fiber, as indicated by the first part of the URL after
dev.azure.com.Note
Project URLs have changed with the release of Azure DevOps Services and now have the format
dev.azure.com/{your organization}/{your project}, but you can still use the existingvisualstudio.comformat. For more information, see VSTS is now Azure DevOps Services.Run
git clonefrom the command prompt.
SSH may display the server's SSH fingerprint and ask you to verify it.
For cloud-hosted Azure DevOps Services, where clone URLs contain either ssh.dev.azure.com or vs-ssh.visualstudio.com, the fingerprint should match one of the following formats:
- MD5:
97:70:33:82:fd:29:3a:73:39:af:6a:07:ad:f8:80:49(RSA) - SHA256:
SHA256:ohD8VZEXGWo6Ez8GSEJQ9WpafgLFsOfLOtGGQCQo6Og(RSA)These fingerprints are also listed in the SSH public keys page.
For self-hosted instances of Azure DevOps Server, you should verify that the displayed fingerprint matches one of the fingerprints in the SSH public keys page.
SSH displays this fingerprint when it connects to an unknown host to protect you from man-in-the-middle attacks.Once you accept the host's fingerprint, SSH will not prompt you again unless the fingerprint changes.
When you are asked if you want to continue connecting, type yes. Git will clone the repo and set up the origin remote to connect with SSH for future Git commands.
Tip
Avoid trouble: Windows users will need to run a command to have Git reuse their SSH key passphrase.
Questions and troubleshooting
Q: After running git clone, I get the following error. What should I do?
Host key verification failed.fatal: Could not read from remote repository.
A: Manually record the SSH key by running:ssh-keyscan -t rsa domain.com >> ~/.ssh/known_hosts
Q: How can I have Git remember the passphrase for my key on Windows?
A: Run the following command included in Git for Windows to start up the ssh-agent process in Powershell or the Windows Command Prompt. ssh-agent will cacheyour passphrase so you don't have to provide it every time you connect to your repo.
If you're using the Bash shell (including Git Bash), start ssh-agent with:
Q: I use PuTTY as my SSH client and generated my keys with PuTTYgen. Can I use these keys with Azure DevOps Services?
A: Yes. Load the private key with PuTTYgen, go to Conversions menu and select Export OpenSSH key.Save the private key file and then follow the steps to set up non-default keys.Copy your public key directly from the PuTTYgen window and paste into the Key Data field in your security settings.
Q: How can I verify that the public key I uploaded is the same key as I have locally?
A: You can verify the fingerprint of the public key uploaded with the one displayed in your profile through the following ssh-keygen command run against your public key usingthe bash command line. You will need to change the path and the public key filename if you are not using the defaults.
You can then compare the MD5 signature to the one in your profile. This check is useful if you have connection problems or have concerns about incorrectlypasting in the public key into the Key Data/passport-photo-maker-key-generator.html. field when adding the key to Azure DevOps Services.
Q: How can I start using SSH in a repository where I am currently using HTTPS?
A: You'll need to update the origin remote in Git to change over from a HTTPS to SSH URL. Once you have the SSH clone URL, run the following command:
You can now run any Git command that connects to origin.
Q: I'm using Git LFS with Azure DevOps Services and I get errors when pulling files tracked by Git LFS.
A: Azure DevOps Services currently doesn't support LFS over SSH. Use HTTPS to connect to repos with Git LFS tracked files.
Q: How can I use a non default key location, i.e. not ~/.ssh/id_rsa and ~/.ssh/id_rsa.pub?
Generate Ssh Key With Different Name
A: To use keys created with ssh-keygen in a different place than the default, you do two things:
- The keys must be in a folder that only you can read or edit. If the folder has wider permissions, SSH will not use the keys.
- You must let SSH know the location of the keys. You make SSH aware of keys through the
ssh-addcommand, providing the full path to the private key.
Generate Ssh Key Putty
On Windows, before running ssh-add, you will need to run the following command from included in Git for Windows:
This command runs in both Powershell and the Command Prompt. If you are using Git Bash, the command you need to use is:
You can find ssh-add as part of the Git for Windows distribution and also run it in any shell environment on Windows.
On macOS and Linux you also must have ssh-agent running before running ssh-add, but the command environment on these platforms usuallytakes care of starting ssh-agent for you.
Q: I have multiple SSH keys. How do I use different SSH keys for different SSH servers or repos?
A: Generally, if you configure multiple keys for an SSH client and connect to an SSH server, the client can try the keys one at a time until the server accepts one.
However, this doesn't work with Azure DevOps for technical reasons related to the SSH protocol and how our Git SSH URLs are structured. Azure DevOps will blindly accept the first key that the client provides during authentication. If that key is invalid for the requested repo, the request will fail with the following error:
For Azure DevOps, you'll need to configure SSH to explicitly use a specific key file. One way to do this to edit your ~/.ssh/config file (for example, /home/jamal/.ssh or C:Usersjamal.ssh) as follows:
Generate Ssh Key Different Name In Word
Q: What notifications may I receive about my SSH keys?
A: Whenever you register a new SSH Key with Azure DevOps Services, you will receive an email notification informing you that a new SSH key has been added to your account.
Q: What do I do if I believe that someone other than me is adding SSH keys on my account?
Generate Ssh Key Github
A: If you receive a notification of an SSH key being registered and you did not manually upload it to the service, your credentials may have been compromised.
Generate Ssh Key Different Name Labels
The next step would be to investigate whether or not your password has been compromised. Changing your password is always a good first step to defend against this attack vector. If you’re an Azure Active Directory user, talk with your administrator to check if your account was used from an unknown source/location.
Top News
- ✔ Generate Cert From Csr And Private Key
- ✔ Batman Arkham Asylum Goty Cd Key Generator
- ✔ Windows Bitlocker Recovery Key Generator
- ✔ Halo Combat Evolved Cd Key Generator
- ✔ Generate Rsa Key Pair Macos
- ✔ Monster Hunter Generations Ultimate Hunter's Hub Key Quests
- ✔ Autocad 2013 Serial Number And Product Key Generator