Simple Django application that adds a new command:
- Aug 12, 2019 This secret key is added to an authenticator app (e.g., Google Authenticator) on a mobile device. The app can then generate TOTP values based on the current time. By default, it generates a new TOTP value every 30 seconds. MinTOTP is a Python tool that can be used to generate TOTP values from a secret key.
- Generating a properly secure SECRETKEY in Django. GitHub Gist: instantly share code, notes, and snippets.
This will generate a new file secretkey.txt containing a random Django secretkey. In your production settings file, replace the hardcoded key by:
You can avoid hardcoding the path of the key by using:
Install
You can install this package from PyPi:
Then you will need to add it to the Django's INSTALLED_APPS setting:
Oct 09, 2016 Simple Django application that adds a new command: python manage.py generatesecretkey -replace secretkey.txt. This will generate a new file secretkey.txt containing a random Django secret key. In your production settings file, replace the hardcoded key. I like having a command to generate a secret key, and the idea of a secret key file. However I think that automatically generating the secret key is going to lead to footgun-ey behavior. This mentions N=1 deployments, however it doesn't account for migrations or the like. Generatesecretkey - Creates a new secret key that you can put in your settings.py module. Graphmodels - Creates a GraphViz dot file. You need to send this output to a file yourself. Great for graphing your models. Pass multiple application names to combine all the models into a single dot file.
You can now use
Run this command once in your local environment, and every time you deploy your app (on the remote host), to make sure the file exists.
-->This article covers how to get started working with Azure Key Vault using the Azure CLI. You can see information on:
- How to create a hardened container (a vault) in Azure
- Adding a key, secret, or certificate to the key vault
- Registering an application with Azure Active Directory
- Authorizing an application to use a key or secret
- Setting key vault advanced access policies
- Working with Hardware security modules (HSMs)
- Deleting the key vault and associated keys and secrets
- Miscellaneous Azure Cross-Platform Command-line Interface Commands
Azure Key Vault is available in most regions. For more information, see the Key Vault pricing page.
Note
This article does not include instructions on how to write the Azure application that one of the steps includes, which shows how to authorize an application to use a key or secret in the key vault.
For an overview of Azure Key Vault, see What is Azure Key Vault?)If you don't have an Azure subscription, create a free account before you begin.
Prerequisites
To use the Azure CLI commands in this article, you must have the following items:
- A subscription to Microsoft Azure. If you don't have one, you can sign up for a free trial.
- Azure Command-Line Interface version 2.0 or later. To install the latest version, see Install the Azure CLI.
- An application that will be configured to use the key or password that you create in this article. A sample application is available from the Microsoft Download Center. For instructions, see the included Readme file.
Getting help with Azure Cross-Platform Command-Line Interface
This article assumes that you're familiar with the command-line interface (Bash, Terminal, Command prompt).
The --help or -h parameter can be used to view help for specific commands. Alternately, The Azure help [command] [options] format can also be used too. When in doubt about the parameters needed by a command, refer to help. For example, the following commands all return the same information:
You can also read the following articles to get familiar with Azure Resource Manager in Azure Cross-Platform Command-Line Interface:
How to create a hardened container (a vault) in Azure
Vaults are secured containers backed by hardware security modules. Vaults help reduce the chances of accidental loss of security information by centralizing the storage of application secrets. Key Vaults also control and log the access to anything stored in them. Azure Key Vault can handle requesting and renewing Transport Layer Security (TLS) certificates, providing the features required for a robust certificate lifecycle management solution. In the next steps, you will create a vault.
Connect to your subscriptions
To sign in interactively, use the following command:
To sign in using an organizational account, you can pass in your username and password.
If you have more than one subscription and need to specify which to use, type the following to see the subscriptions for your account:
Specify a subscription with the subscription parameter.
For more information about configuring Azure Cross-Platform Command-Line Interface, see Install Azure CLI.
Create a new resource group
When using Azure Resource Manager, all related resources are created inside a resource group. You can create a key vault in an existing resource group. If you want to use a new resource group, you can create a new one.
The first parameter is resource group name and the second parameter is the location. To get a list of all possible locations type:
Register the Key Vault resource provider
You may see the error 'The subscription is not registered to use namespace 'Microsoft.KeyVault' when you try to create a new key vault. If that message appears, make sure that Key Vault resource provider is registered in your subscription. This is a one-time operation for each subscription.
Create a key vault
Use the az keyvault create command to create a key vault. This script has three mandatory parameters: a resource group name, a key vault name, and the geographic location.
To create a new vault with the name ContosoKeyVault, in the resource group ContosoResourceGroup, residing in the East Asia location, type:
The output of this command shows properties of the key vault that you've created. The two most important properties are:
- name: In the example, the name is ContosoKeyVault. You'll use this name for other Key Vault commands.
- vaultUri: In the example, the URI is https://contosokeyvault.vault.azure.net. Applications that use your vault through its REST API must use this URI.
Your Azure account is now authorized to perform any operations on this key vault. As of yet, nobody else is authorized.
Adding a key, secret, or certificate to the key vault
If you want Azure Key Vault to create a software-protected key for you, use the az key create command.
If you have an existing key in a .pem file, you can upload it to Azure Key Vault. You can choose to protect the key with software or HSM. This example imports the key from the .pem file and protect it with software, using the password 'hVFkk965BuUv':
You can now reference the key that you created or uploaded to Azure Key Vault, by using its URI. Use https://ContosoKeyVault.vault.azure.net/keys/ContosoFirstKey to always get the current version. Use https://[keyvault-name].vault.azure.net/keys/[keyname]/[key-unique-id] to get this specific version. For example, https://ContosoKeyVault.vault.azure.net/keys/ContosoFirstKey/cgacf4f763ar42ffb0a1gca546aygd87.
Add a secret to the vault, which is a password named SQLPassword, and that has the value of 'hVFkk965BuUv' to Azure Key Vaults.
Reference this password by using its URI. Use https://ContosoVault.vault.azure.net/secrets/SQLPassword to always get the current version, and https://[keyvault-name].vault.azure.net/secret/[secret-name]/[secret-unique-id] to get this specific version. For example, https://ContosoVault.vault.azure.net/secrets/SQLPassword/90018dbb96a84117a0d2847ef8e7189d.
Import a certificate to the vault using a .pem or .pfx.
Let's view the key, secret, or certificate that you created:
- To view your keys, type:
- To view your secrets, type:
- To view certificates, type:
Registering an application with Azure Active Directory
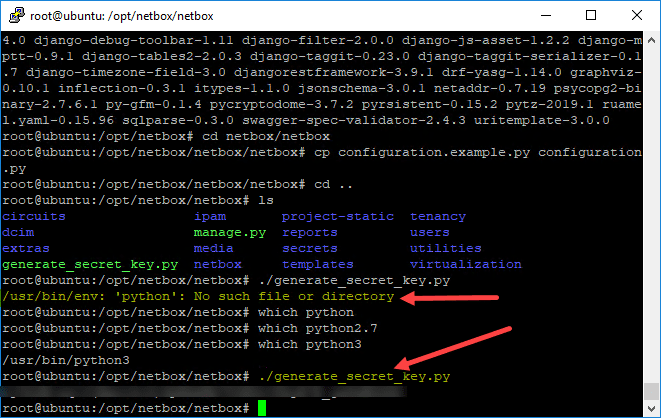
Generate Django Secret Key Command Line Code
This step would usually be done by a developer, on a separate computer. It isn't specific to Azure Key Vault but is included here, for awareness. To complete the app registration, your account, the vault, and the application need to be in the same Azure directory.
Applications that use a key vault must authenticate by using a token from Azure Active Directory. The owner of the application must register it in Azure Active Directory first. At the end of registration, the application owner gets the following values:
- An Application ID (also known as the AAD Client ID or appID)
- An authentication key (also known as the shared secret).
The application must present both these values to Azure Active Directory, to get a token. How an application is configured to get a token will depend on the application. For the Key Vault sample application, the application owner sets these values in the app.config file.
For detailed steps on registering an application with Azure Active Directory you should review the articles titled Integrating applications with Azure Active Directory, Use portal to create an Azure Active Directory application and service principal that can access resources, and Create an Azure service principal with the Azure CLI.
To register an application in Azure Active Directory:
Authorizing an application to use a key or secret
To authorize the application to access the key or secret in the vault, use the az keyvault set-policy command.
For example, if your vault name is ContosoKeyVault, the application has an appID of 8f8c4bbd-485b-45fd-98f7-ec6300b7b4ed, and you want to authorize the application to decrypt and sign with keys in your vault, use the following command:
To authorize the same application to read secrets in your vault, type the following command:
Setting key vault advanced access policies
Use az keyvault update to enable advanced policies for the key vault.
Enable Key Vault for deployment: Allows virtual machines to retrieve certificates stored as secrets from the vault.
Enable Key Vault for disk encryption: Required when using the vault for Azure Disk encryption.
Enable Key Vault for template deployment: Allows Resource Manager to retrieve secrets from the vault.
Working with Hardware security modules (HSMs)
For added assurance, you can import or generate keys from hardware security modules (HSMs) that never leave the HSM boundary. The HSMs are FIPS 140-2 Level 2 validated. If this requirement doesn't apply to you, skip this section and go to Delete the key vault and associated keys and secrets.
To create these HSM-protected keys, you must have a vault subscription that supports HSM-protected keys.
Generate Django Secret Key Command Line Video
When you create the keyvault, add the 'sku' parameter:
You can add software-protected keys (as shown earlier) and HSM-protected keys to this vault. To create an HSM-protected key, set the Destination parameter to 'HSM':
You can use the following command to import a key from a .pem file on your computer. This command imports the key into HSMs in the Key Vault service:
The next command imports a 'bring your own key' (BYOK) package. This lets you generate your key in your local HSM, and transfer it to HSMs in the Key Vault service, without the key leaving the HSM boundary:
For more detailed instructions about how to generate this BYOK package, see How to use HSM-Protected Keys with Azure Key Vault.
Deleting the key vault and associated keys and secrets
If you no longer need the key vault and its keys or secrets, you can delete the key vault by using the az keyvault delete command:
Or, you can delete an entire Azure resource group, which includes the key vault and any other resources that you included in that group:
Miscellaneous Azure Cross-Platform Command-line Interface Commands
Django Command Line
Other commands that you might find useful for managing Azure Key Vault.
This command lists a tabular display of all keys and selected properties:
This command displays a full list of properties for the specified key:
Django Custom Command
This command lists a tabular display of all secret names and selected properties:
Here's an example of how to remove a specific key:
Here's an example of how to remove a specific secret:
Django Add Command
Next steps
Django Secret Key Generator
For complete Azure CLI reference for key vault commands, see Key Vault CLI reference.
For programming references, see the Azure Key Vault developer's guide
For information on Azure Key Vault and HSMs, see How to use HSM-Protected Keys with Azure Key Vault.